“All malware is based on deception” Sun Tzu by Chris
A computer malware is something that creeps into our computers, and until something bad happens we just assume our free version of AV will take care of it and we can move on with our busy life’s.
The sad truth is that most people think in a similar fashion. The problem really escalates when we lose our sensitive data such as documents and pictures or even identity. In these short series of educational articles, I will talk about most common computer malware, type of attacks and what we can do to minimize our risks. After all its all about risk management. I believe that it’s our own responsibility to know what type of dangerous are in the world. Once we know what’s out there, we can prepare by reading, googling, or even YouTube a topic and when times comes we should know What To Do, and Not To Do in a given situation. After all we teach our children not talk to strangers or not to play with matches. Same principal applies to etiquette on all computers systems and worldwide web.
Let’s starting with a definition; a computer malware according to Wikipedia is “any software intentionally designed to cause damage to a computer, server or computer network” Simple right? Sure, it is, but its not enough to be safe out there. We need to understand what are some vectors of attack hackers use to deceive us in getting infected.
There are many different types of malware. Each has unique wicked design, and every year hackers are becoming more creative. However, in most part, we can categorize all malware into the following groups which I will explain in a bit more details:
- Viruses
- Worms
- Trojan
- Rootkit
- Ransomware
- Keylogger
- Adware
- Spyware
- Hybrid
1. Computer Virus
A virus by a definition in order to survive needs to attach itself to a host. Once the host application that the virus is attached to is executed, the virus will seek other host in order to replicate. At some point and time, the virus will activate and deliver its malicious payload. The results can be various depending on a virus type.
Examples of different types of viruses
- File Infectors Virus
- Macro virus
- Boot sector virus
- Stealth, Polymorphic and Armored Viruses
- Resident virus
- Logic Bomb virus
- Multipartite Virus
File Infecting virus infects executable files with .exe or .com extensions, and it’s probably the most common type of virus. Most end users think of a computer virus as a file-infecting virus.
Macro virus mostly residues inside Microsoft Word or Excel office suites. They use embedded applications feature to use powerful macro language, which hides inside office documents, so the moment you open one of those files the virus automatically executes as well.
Boot sector virus infects boot sector of a removable memory or Master Boot Record (MBR). Those are first sectors of a disk that identifies how and where the operating system is located, so than it can be loaded into the computer’s memory. The boot sector viruses really gained traction with floppy disks. I still remember times when brand new floppy would come straight from a store with pre-infected viruses. Now a days we don’t have floppy drive but any thump drive can be a host of such a virus.
Resident virus is like unwanted tenant. Just because you terminated the original infected file, it will still embed itself in to the computers random-access memory (RAM) and continue to operate. For the same reason you might have seen an option in your AV to not only scan your HDD but also RAM.
Stealth viruses are often Resident because they need to hide in RAM in order to intercept OS read and write function to storage media. This means that they can make the infected files or sectors look uninfected. A lot of sophisticated malware uses stealth mode techniques in order to residue on your system undetected. Time when you knew where infected are mostly gone, and only time you might know you got infected is with Ransomware malware.
Polymorphic virus can transform itself into different forms by changing its code or encrypting itself thus making itself very difficult for the antivirus program to detect it. The reason why is because all AV use signature-based database in order to detect and eradicate malware from the system. This type of virus is extremely sophisticated and very often impossible to locate. If you believe you might have been infected with one, the only option really is performing a deep level format and reinstall operating system from scratch.
Armored virus use various techniques to make the attempts of tracing or examining the code more difficult. The reason why is so the information security researches won’t have it easy to reverse engineer the malware. After all some hacking organizations can spend quite a lot of time perfecting their malicious code.
Logic Bomb virus will only execute when a specific condition is met. One common example would be disgruntled employee who upon termination from the company will schedule deletion of some critical files. Another example could be such as upcoming Black Friday. Watch out for bogus web sites that can easily trick you into getting infected.
Multipartite Virus infects and replicate in multiple ways. For instance, it can attack a boot sector and executable files simultaneously, thus causing more serious damage than any other virus.
Good news is that pure computer viruses are not as common today, as they where lets say 10 years ago. Depending on the sources, they occupy probably less than 10 percent of all malware. Nevertheless its not a force you want to reckon with, ten percent is still millions of victims word wide.

Example: ILOVEYOU

2. Computer Worm
A computer worm very often gets categorized as virus, but in my opinion that is very misleading mistake. In comparison to a virus a worm does not need to attach itself to a host in order to replicate and cause mayhem. A worm is a standalone malware that looks for vulnerabilities in computers and network systems in order to replicate. For that reason, it is extremely important to keep your operating system and hardware patched. Worms can be a relatively simple code that is designed to make copies of itself over and over thus depleting system resources, such as hard drive space, memory or bandwidth of a computer network. But then again, a worm can be very sophisticated software that once finds and penetrate its target it can inject additional malicious software in order to perform higher level functions. For instance, make a victim join a Botnet and be part of distributed denial of service (DDoS) attack.
Botnet: “a network of private computers infected with malicious software and controlled as a group without the owners’ knowledge, e.g., to send spam messages.” wiki
DDoS: “attack occurs when multiple systems flood the bandwidth or resources of a targeted system, usually one or more web servers” wiki
Example: Stuxnet

3. Trojan
You most likely heard about Trojan horse, and if you did not and don’t want to lose yourself into a Greek mythology, at the minimum watch a movie “Troy” with Brat Pit. The story talks about Greeks waging a war again independent city of Troy. On the end, sorry spoiler alert – Greek soldiers, by hiding inside a giant wooden horse manage to get in to the heavily fortification city of Troy. The irony of the story is that Trojans willingly accepted the horse as a gift of their victory; but at night Greek soldiers got out and let the rest of their army in, and slaughter everyone inside the city.
A Trojan malware is often used in a Social Engineering, which by the way is one of my favorite separate topic by itself; Hackers often use different techniques to gain trust and make the end user to execute a malicious software on their otherwise secure systems. A Trojan unlike a computer virus is not designed to self-replicate.
Social Engineering: “psychological manipulation of people into performing actions or divulging confidential information”. wiki
Example: Zeus

4. Rootkit
A rootkit is a group of tools that is intended to gain elevated system privilege and hide itself from being detected. Once injected into victims’ systems, hackers use it to install a keylogger, spyware or other malicious code. Most rootkits are delivered using a Trojan, by opening deceiving email attachment or clicking on a bait link. The name Root derives from Unix/Linux OS which stands for an Admin account, and the word Kit stand for collection of software that make the rootkit work.
In general, rootkits can be divided into two separate categories: User Mode and Kernel Mode. There is significant difference between the two, because a user mode can be relatively easily eradicated; However, the Kernel Mode chills along the kernel of the OS, which is a core of a computer’s operating system, which then gives it a complete control over anything and everything in that system. In conclusion, it can be able to manipulate all the system resource without being detected.
Good Read:
https://www.csoonline.com/article/3222066/malware/how-to-detect-and-remove-a-rootkit-in-windows-10.html
https://resources.infosecinstitute.com/rootkits-user-mode-kernel-mode-part-2/
5. Ransomware
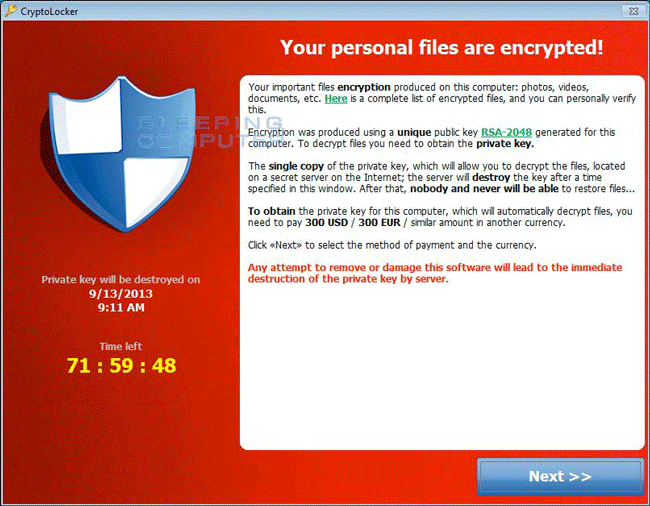
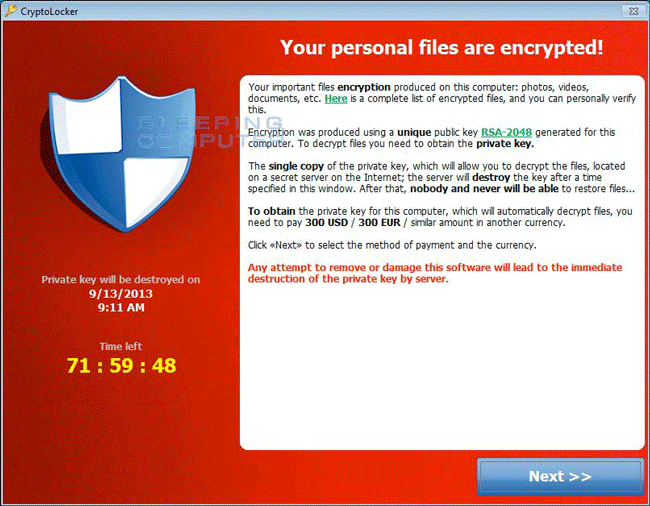
A ransomware is a crypto malware that is designed to extort money from individuals or companies. Not a new concept, but it has definitely gained traction along with a popularity of a cryptocurrency such as bitcoin. Last year, or maybe it was a year before, IBM performed a study, which concluded that a ransomware attacks have increased by 6,000%, and about 75% of all victims pay up. In general, there are two categories of ransomware: Locker and Crypto ransomware.
Locker ransomware: Deny access to a victim’s own device but in most part does not affect an operating system or a user’s data. As a result, attacker uses various social engineering techniques such as pretending to be from government authorities.
Crypto ransomware: Is much worse malware than the locker ransomware. The infection prevents access to a victim’s data by encrypting all valuable data, and in return on having it unencrypted you need to pay ransomware. That’s when a cryptocurrency such as bitcoin come in handy. Personally, I have been also affected by having my shared Onedrive encrypted when one my coworker opened an email attachment with a ransomware malware. Thankfully I had a backup. Hopefully you have one a well.
Good Read:
http://www.symantec.com/content/en/us/enterprise/media/security_response/whitepapers/the-evolution-of-ransomware.pdf
Example: Cryptowall
6. Keylogger
A keylogger is a program that without user consent records and tracks all keyboard strokes which then the can be obtained by the unauthorized person. The key strokes can obviously capture stuff like letters to Santa, but also all other sensitive information such as credit card information or passwords. Now very important part that I would like to emphasize: I did not say a Hacker. The reason why is because keyloggers are vastly available programs that anybody who know how to install a web browser can potentially deploy one. The reason why is because they are often used for legitimate use by IT admins or even concerned parents. Nevertheless majority of them are used for criminal purposes.
Sample of keyloggers
https://lifehacker.com/how-to-install-a-windows-keylogger-1829986319
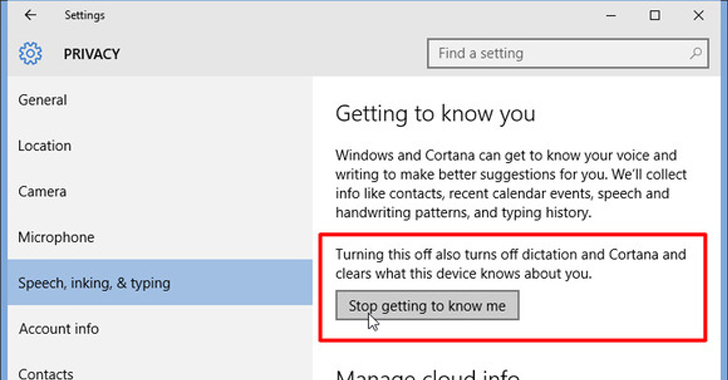
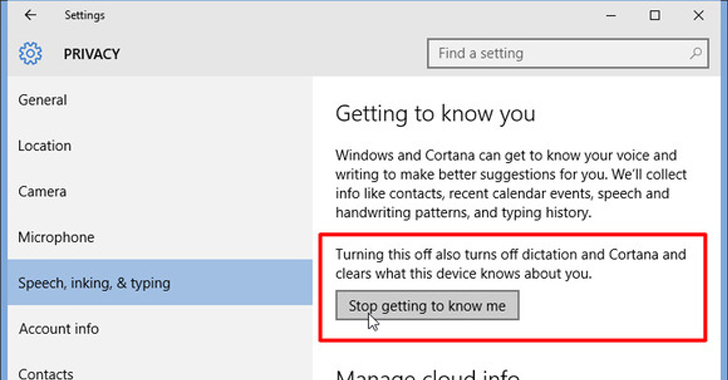
Example: Did you know Windows10 has built in keylogger?
7. Adware
In simple terms Adware is a forced advertisement projected on your screen. Most attacks are made via a web browser but can also be done during installation of a free software when unwanted PUP (potentially unwanted program) is being piggybacked. The advertisement can have many forms such as pop-ups, banners, audio and video. In many cases they are just more of annoyance than a real threat. Nevertheless, most adware now a days also steal your personal information such as web history etc..
My favorite program for ad-blocking and content-filtering is an open-source and cross-platform web extension called uBlock Origin. Just google one for you web browser.
Example: uBlock Origin
8. Spyware
Spyware same as real spies, once infiltrate your system, quietly run in the background collecting personal information, take screen shots, capture key strokes or steal your credit card information. Furthermore, stuff like social security or credit card info normally is sold for profit on a “deep web”. However, in most part a spyware is used to for tracking and storing internet user activities on a web, and serving adware.
Example: Famous program distributed with Spyware

8. Hybrids
The truth is that now a days most malware can be a combination of a Trojan, Worm and a Virus. They can use Trojan to get into your system, spread true the network using a Worm and use Viruses capabilities of being Polymorphic and Multipartie.
Now you can continue to use your AV by frequently scanning your hard drive, but the truth is that unless you are skilled in finding and analyzing malware the only option is to stay proactive and minimize the possibility of getting infected in a first place.
In my next article I will cover some basic good information security practices that anyone can follow. Please stay tuned and don’t forget to comment.
Read More →